
Practice Problem 2.18 (solution page 149)
In Chapter 3, we will look at listings generated by a disassembler, a program that converts an executable program file back to a more readable ASCII form. These files contain many hexadecimal numbers, typically representing values in two’s- complement form. Being able to recognize these numbers and understand their significance (for example, whether they are negative or positive) is an important skill.
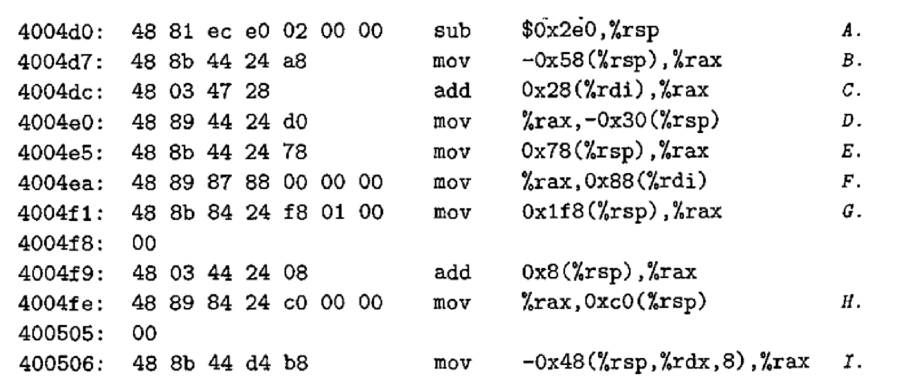
For the lines labeled A-I (on the right) in the following listing, convert the hexadecimal values (in 32-bit two’s-complement form) shown to the right of the instruction names (sub, mov, and add) into their decimal equivalents:
Want to see the full answer?
Check out a sample textbook solution
Chapter 2 Solutions
Computer Systems: A Programmer's Perspective (3rd Edition)
Additional Engineering Textbook Solutions
Digital Fundamentals (11th Edition)
Java: An Introduction to Problem Solving and Programming (8th Edition)
Introduction to Java Programming and Data Structures, Comprehensive Version (11th Edition)
Database Concepts (7th Edition)
Experiencing MIS
Concepts of Programming Languages (11th Edition)
- Computer Science For LZ78: Task 1 - In order to compute the tuples of some text files, create a computer program using Java. Calculate how many tuples are computed. You should compress and decompress the text without any loss so check original text with decompressed text if they are same. Represent your tuples into bits’ representation and calculate for each file the compression ratio.Do above steps by proceeding assigned algorithm in reverse order. (From right to left) Regarding to above result: a) Compare the number of tuples b) Compare compression ratio (Use Huffman encoding Algorithm)arrow_forwardProblem 1 (Ransom Note Problem) in python A kidnapper kidnaps you and writes a ransom note. He does not write it by hand to avoid having his hand writing being recognized, so he uses a magazine to create a ransom note. We need to find out, given the ransom string and magazine string, is it possible to create a given ransom note. The kidnapper can use individual characters of words. Here is how your program should work to simulate the ransom problem: your program should prompt the user to enter a long String to represent the magazine and another short String to represent the required ransom note. your program needs to check if the magazine string contains all required characters in equal or greater number present in the ransom note. your program should print true if it is possible to create the given ransom note from the given magazine, and print false otherwise. Break up your code into a set of well-defined functions. Each function should include a comment block that briefly describes…arrow_forward2, Towers of Hanoi Problem. (10 points) The Towers of Hanoi is a famous problem for studying recursion in computer science and searching in artificial intelligence. We start with N discs of varying sizes on a peg (stacked in order according to size), and two empty pegs. We are allowed to move a disc from one peg to another, but we are never allowed to move a larger disc on top of a smaller disc. The goal is to move all the discs to the rightmost peg (see figure). To solve the problem by using search methods, we need first formulate the problem. Supposing there are K pegs and N disk. Answer the following questions. (1) Determine a state representation for this problem. (4points) (2) What is the size of the state space? (3 points) (3) Supposing K=3, N=4, what is the start state by using your proposed state representation method and what is the goal state? (3 points)arrow_forward
- Problem #2: A number in base 2 (binary) is a number such that each of its digits is 0 or 1. To convert from binary to decimal (base 10), the digits starting from the right are multiplied by powers of 2 (starting at 0) and added. For example, the value in decimal of 10011 is calculated as follows: 1 x2°+1 x2+ 0 x22+ 0 x23+ 1 x2*=19 Write a program that reads from the user a 5-digit integer representing a value in binary and displays its equivalent value in decimal. Note that if the user enters an integer which digits are other than 0 or 1, the program displays a message stating that the number is invalid. Sample Run 1: Enter a 5-digit integer made of Os and 1s: 10011 10011 in decimal is l9 Sample Run 2: Enter a 5-digit integer made of Os and 1s: 13001 13001 is not validarrow_forwardProblem 1 Modify Problem 1.py by adding additional lines of code so that it solves the following problem: Determine whether a given number is even and part of the Fibonacci Sequence. The Fibonacci Sequence is as follows 0, 1, 1, 2, 3, 5, 8, 13... For more information about Fibonacci sequences Click here the sequence is comprised exclusively of positive integers. Hint 1: A positive number, n, is part of the Fibonacci sequence if either (5n^2 + 4) or (5n^2 - 4) is a perfect square. That is, if the square root of either (5n^2 + 4) or (5n^2 - 4) is a whole number, then n is a perfect square, and thus a Fibonacci number. Hint 2: Recall that multiple conditions can be checked in one statement. For example, if (condition 1) and (condition 2) and (condition 3): # do some action If a number is even, positive, and part of the Fibonacci sequence, your code should print "Yes". If any one of these conditions is not met, your code should print "No". If your input is number = 2 or 34 or 144, the…arrow_forward(python) 11. Create a function based on the following information: There is a list which contains integers or other nested lists which may contain yet more lists and integers which then… you get the idea. You should put all of the integer values into one flat list. The order should be as it was in the original list with string representation from left to right. [1, 2, [ 3, 4], [5,6]] ==> [1, 2, 3, 4, 5, 6] Input data: A nested list with integers. Output data: Nothing to output Return: The one-dimensional list with integers.arrow_forward
- [C Program] 3. Float Count-off by CodeChum Admin Counting off a list of float numbers is hard when you speak it, but not when you code it! Don't believe me? Then let's try coding just that! Instructions: An array containing 30 predefined float values are already provided for you in the code editor. Print each of the element out in separate lines, starting from the last array element down to the first. Each outputted value must also only show up to two decimal places. Output Multiple lines containing a float number. 2.41 143.00 3.14 3.12 0.00 -321.12 -414.12 12312.10 4.10 2.42 . . . ------------------------------------ #include<stdio.h> int main(void) { float nums[30] = { 1.4, 1.2054, 2.2, 2.5, 3.66, 3.0, 4.024, 4.00001, 5.5, 5.10, 1, 2, 3, 4, 5, -1.11, -1.111, -1.1111, -1.11111, -1.111111, 2.421, 4.1, 12312.1, -414.123, -321.12, 0, 3.123, 3.14, 143, 2.412 }; return 0; } [C Program] [C…arrow_forward[C Program] 3. Float Count-off by CodeChum Admin Counting off a list of float numbers is hard when you speak it, but not when you code it! Don't believe me? Then let's try coding just that! Instructions: An array containing 30 predefined float values are already provided for you in the code editor. Print each of the element out in separate lines, starting from the last array element down to the first. Each outputted value must also only show up to two decimal places. Output Multiple lines containing a float number. 2.41 143.00 3.14 3.12 0.00 -321.12 -414.12 12312.10 4.10 2.42 . . . ---------------------------------- #include<stdio.h> int main(void) { float nums[30] = { 1.4, 1.2054, 2.2, 2.5, 3.66, 3.0, 4.024, 4.00001, 5.5, 5.10, 1, 2, 3, 4, 5, -1.11, -1.111, -1.1111, -1.11111, -1.111111, 2.421, 4.1, 12312.1, -414.123, -321.12, 0, 3.123, 3.14, 143, 2.412 }; return 0; }arrow_forwardProblem 2 (5 pts) Write a Python program that plays the game Ro-Sham-Bo (a.k.a., Rock, Paper, Scissors) for a player and a computer opponent. The player selects one of the options listed in a console prompt, then the computer randomly selects an option as well. The winner of the game is determined as follows: Rock beats Scissors - Scissors beats Paper - Paper beats Rock The same selection results in a tie. Your program must do the following: Prompt the player to enter a selection in the console. Provide instructions to user on what is a valid input. For example, you can have the integers 1, 2, and 3 represent the selection, or use the words rock, paper, scissors, etc. Check that the user entered valid input. If the entry is invalid, the program needs to inform the user of the invalid input and can end, or re-prompt the user for their entry. Generate a random selection for the computer's choice. You can use a random integer and follow the same rules as was stated to the user. - Display…arrow_forward
- (python) 10. Create a function based on the following information: Your mission is to encrypt a secret message (text only, without special chars like "!", "&", "?" etc.) using Caesar cipher where each letter of input text is replaced by another that stands at a fixed distance. For example ("a b c", 3) == "d e f" Input: A secret message as a string (lowercase letters only and white spaces) and number to move text Output: The same string, but encrypted Return: The same string, but encryptedarrow_forwardHuffman Code[Problem Description]For an English article, the frequency of occurrence of 26 lowercase letters is counted, and then they are encoded by Hoffman code.[Basic Requirements]1) Read the original text file from the file and display the text on the screen..2) Output the number of occurrences of 26 English lowercase letters, and the corresponding Hoffman code... Below is the data to be displayed At present, most of the dynamic sign language recognition is only for sign language words,the continuous sign language sentence recognition research and the corresponding results are less, because the segmentation of such sentence is very difficult. In this paper, a sign languagesentence recognition algorithm is proposed based on weighted key frames. Key frames can be regardedas the basic unit of sign word, therefore, according to the key frames we can get related vocabularies, and thus we can further organize these vocabularies into meaningful sentence. Such work can avoid the…arrow_forward[Job sequencing using deadlines]Let us suppose that there are n jobs (J1, J2, … Jn) each of which takes a unit oftime to be processed by a machine and there is just one single machine to processthe jobs. Let us suppose that (d1, d2, d3, …dn) are the deadlines in units of times to complete the jobs and (p1, p2, p3, …pn) are the profits earned if the jobs are processed within the deadline. The objective is obviously to select those jobs and complete them within their deadlines so that maximum profit is earned.Design a greedy method to obtain the optimal sequence of jobs that will earnmaximum profits. Demonstrate it on the case where there are four jobs, with n = 4,deadlines given by (d1 = 2, d2 = 1, d3 = 3, d4 = 1) and profits earned as (p1 = 100,p2 = 20, p3 = 50, p4 = 40).arrow_forward
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education





